COVID-19 won’t be here forever, but cybercriminals will!
Leveraging the COVID-19 situation, cybercriminals are targeting SMEs and even large enterprises to steal valuable information. Many reports claim that cybercrimes have doubled in the last couple of months.
The healthcare industry is one of the latest victims of cybercriminals. According to Accenture, the healthcare industry has witnessed around 41% increase in cyberattacks. The report also says that the healthcare industry on average experiences 130 data breaches in a year.
However, as a healthcare IT consultant, I have recently noticed that healthcare organizations are ramping up their efforts to safeguard patient data. And for that, they are deploying many technologies, solutions and unique cost-effective ideas.
The technologies, solutions and ideas healthcare startups are deploying are so effective that other startups can learn cybersecurity lessons from healthcare startups. Today, in this blog, I will share the same. I will list down 6 cybersecurity lessons learned from healthcare organizations in 2020 during COVID-19.
How are healthcare startups avoiding cybercriminals? (Learning from other startups!)
Avoiding cybercriminals or ensuring data security is not a task, it is the process. And a process is always more complicated than a task. But here is how healthcare organizations are streamlining the process, the cybersecurity process.
- Determine the cybersecurity risks level
Not all healthcare startups are on the radar of cybercriminals. Thus, it is a rational idea to determine the possibility of a cyberattack or to determine the cybersecurity risks level. This process enables organizations to know the threat level – whether they are on the radar of cybercriminals or not.
To find the cybersecurity risks level, healthcare organizations simply link the type of data they store to the motive of cybercriminals. For instance, if a healthcare organization stores medical images of patients and not the patient’s personal and financial data, they should not invest more in cybersecurity.
But if a healthcare organization stores many valuable data of the patients, accommodates less-trained staff and works with legacy networks, they should worry about cybersecurity as their cybersecurity risk is high.
Learning for other startups: You should invest only after confirming that you are the potential target! If you do not store any crucial data, you don’t have to allocate your resources to cybersecurity.
- Find the loopholes through technical assessment
A network has many open doors or errors which work as the opportunities for hackers to get access to databases. They usually scan the network and attack the ‘fragile part’. Thus, it is important to find the loopholes in the network and fix it to close the entry doors for the cybercriminals.
Carrying out the technical assessment is the best way to find loopholes in the network. It is designed to yield the vulnerability in the network. A technical assessment does not only aim to find the vulnerabilities, but it also aims to quantify and prioritize the vulnerabilities.
So, now when cybersecurity experts know the loopholes which cybercriminals can leverage to attack, the cybersecurity experts can easily avoid the attack by fixing the loopholes.
Learning for other startups:
This is the best method to avoid cyber attacks. You should find the open doors in your network and close it to prevent the undetected entry of hackers into your network.
- Software configuration assessment
A healthcare organization uses a number of software to streamline operations. They also use a lot of complex software. Sometimes, the poor configuration of these complex software creates easy paths for cybercriminals to attack the enterprise network as cybercriminals are many times using software to get access to the network or a server.
Learning for other startups:
While installing software on a computer device connected in the enterprise network, make sure the authenticity of the software and do not change the installation setting or software setting without the proper knowledge.
- Quick incident response
Regardless of the efforts healthcare organizations put to safeguard the network, cybercriminals many times find ways to penetrate the security measures. In such a scenario, only a quick incident response is hope.
Healthcare organizations always pay extra heed to incident response. They form a team which quickly takes control over the network and close the paths for attackers before they cause havoc.
The incident response team utilizes many security tools to monitor the network in real-time. If they identify any unusual activity or the system alerts them, they quickly put best practices to work to prevent cybercriminals from getting system access.
Learning for other startups:
Always work best but prepare for the worst. Cybercriminals can anytime, anyhow bypass the security of your system. So, be proactive and prepared.
- Train the staff
Generally, staff working in the healthcare organization lacks the knowledge of the cybersecurity which leads them to click on any malicious links or commit any costly mistake. Thus, healthcare organizations are putting emphasis on staff training. They give basic knowledge about cybersecurity and their deployed network to the staff and keep testing the staff’s cybersecurity knowledge after a fixed interval.
Learning for other startups:
If your staff does not follow cyber hygiene, things can easily go messy as staff members have network access and they spend the majority of their time around it.
- Always deploy feature-packed security solution including firewall
To ensure cybersecurity, deploying software security solutions as well as hardware security solutions is the basic requirement. But a premium security solution works more precisely and efficiently than an affordable security solution. Thus, healthcare organizations generally deploy premium feature-packed security solutions, especially a firewall.
A feature-packed firewall costs a bit more than the basic firewall. But a feature-packed firewall is worth the money. It does not only safeguard the enterprise network but offers many flexibilities and real-time network data to the admin.
For instance,
- Admin can know the connected network and find the data usage of each network.
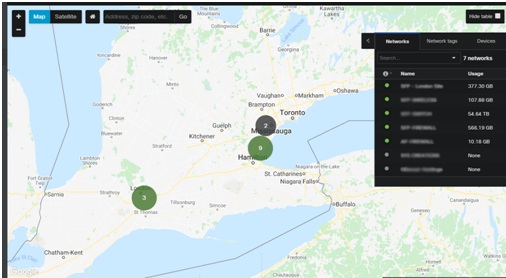
- Admin can know the top sources of threats to a network.

- Admin can know the most affected network.
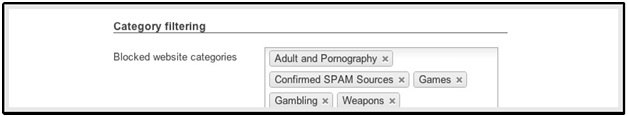
- Admin can impose content filtering to prevent users from opening irrelevant sites.
- Admin can know every single activity of the users on that network.
Learning for other startups:
An ‘affordable security solution’ is the myth, actually!
In a nutshell:
Cybersecurity is the challenge for any startup serving in any industry. An ever-increasing number of cybersecurity attacks clearly depicts that it is a much bigger problem for startups than COVID-19.
However, there is one industry that is pulling out all dots to curb the coronavirus as well as cyberattacks. In this blog, we have discussed 6 ways of how healthcare organizations are safeguarding crucial patient data.
These ways are,
- Confirm the level of cyberattack risk
- Find the loopholes in the network and fix it
- Do not configure the software without proper knowledge
- Form an incident response team
- Train the staff
- Opt for feature-packed security solutions


